Remote SSH IoT has become an essential tool for businesses and individuals looking to manage devices remotely with security and efficiency. As the Internet of Things (IoT) continues to evolve, the need for secure and reliable remote access solutions grows. Remote SSH IoT allows users to connect to IoT devices from anywhere in the world, enabling real-time monitoring, troubleshooting, and management. With the rise of remote work and smart technologies, this solution is more critical than ever.
In today's hyper-connected world, IoT devices are deployed across industries, from healthcare to manufacturing, and even in smart homes. However, ensuring secure access to these devices is a challenge that Remote SSH IoT addresses effectively. By leveraging SSH protocols, users can establish encrypted connections, safeguarding sensitive data and operations. This article will explore the best Remote SSH IoT solutions, their features, and how they can benefit your setup.
Whether you're a tech enthusiast, a business owner, or an IT professional, understanding the best Remote SSH IoT solutions can help you optimize your operations. From setting up secure connections to troubleshooting common issues, this guide will provide you with actionable insights and expert recommendations. Let's dive in!
Read also:Ullu Web Series New 2024 The Ultimate Guide To Indias Hottest Streaming Sensation
Table of Contents:
- Introduction to Remote SSH IoT
- Benefits of Using Remote SSH IoT
- Top Remote SSH IoT Solutions
- Choosing the Right Remote SSH IoT Solution
- Securing Your Remote SSH Connections
- Common Issues and Troubleshooting
- Case Studies: Real-World Examples
- Future of Remote SSH IoT
- Best Practices for Remote SSH IoT
- Conclusion and Next Steps
Introduction to Remote SSH IoT
Remote SSH IoT refers to the practice of using Secure Shell (SSH) protocols to remotely access and manage IoT devices. SSH is a cryptographic network protocol that provides secure communication over unsecured networks. It is widely used in IT environments for its ability to encrypt data, authenticate users, and protect against unauthorized access.
With the proliferation of IoT devices, the demand for secure remote access solutions has surged. Remote SSH IoT enables users to connect to devices located anywhere in the world, ensuring seamless management and monitoring. This is particularly important for industries that rely on IoT devices for critical operations, such as healthcare, agriculture, and manufacturing.
The integration of SSH with IoT devices offers several advantages, including enhanced security, ease of use, and scalability. By leveraging Remote SSH IoT, users can perform tasks such as firmware updates, configuration changes, and data retrieval without being physically present at the device location.
Benefits of Using Remote SSH IoT
Remote SSH IoT offers numerous benefits that make it an attractive solution for managing IoT devices. Below are some of the key advantages:
- Enhanced Security: SSH encrypts all data transmitted between the user and the IoT device, ensuring that sensitive information remains protected from unauthorized access.
- Cost-Effectiveness: By eliminating the need for physical presence, Remote SSH IoT reduces travel costs and improves operational efficiency.
- Scalability: SSH can handle multiple devices simultaneously, making it suitable for large-scale IoT deployments.
- Reliability: SSH connections are stable and reliable, ensuring uninterrupted access to IoT devices even in challenging network conditions.
- Easy Integration: SSH can be easily integrated with existing IT infrastructures, making it a versatile solution for various industries.
These benefits make Remote SSH IoT an ideal choice for businesses and individuals seeking secure and efficient remote access solutions.
Read also:Filmyflypi Your Ultimate Guide To Streaming Movies Online
Top Remote SSH IoT Solutions
Solution 1: SSH Tunneling
SSH tunneling is one of the most popular methods for implementing Remote SSH IoT. It involves creating a secure tunnel between the user's device and the IoT device, ensuring that all data transmitted through the tunnel is encrypted and protected.
SSH tunneling can be used for various purposes, such as accessing web applications, transferring files, and managing databases. Its flexibility and ease of use make it a preferred choice for many users. Additionally, SSH tunneling can be configured to work with firewalls and other security measures, enhancing its effectiveness in securing IoT devices.
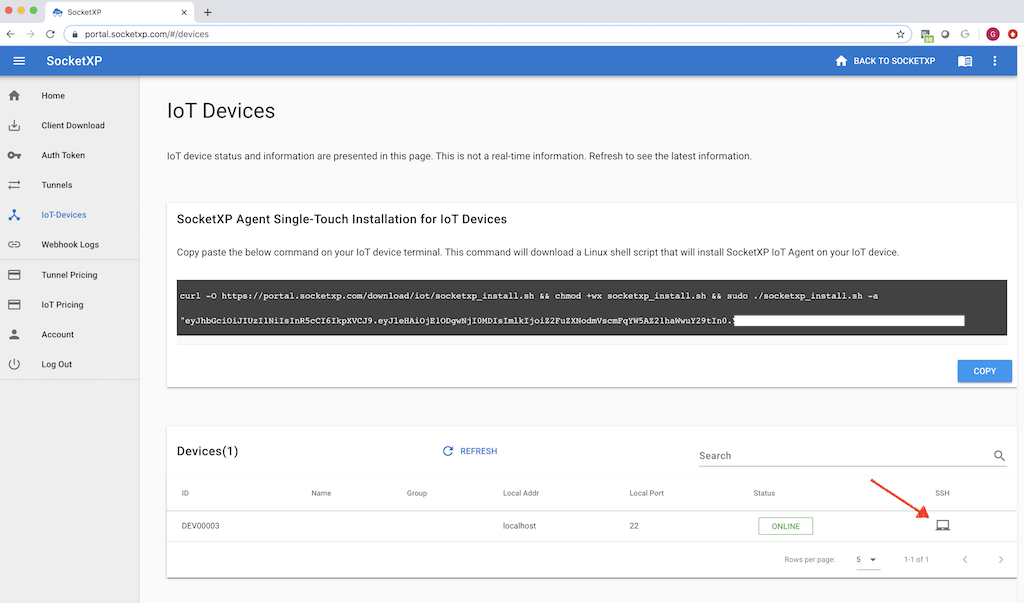
Solution 2: Cloud-Based SSH
Cloud-based SSH solutions offer a modern approach to Remote SSH IoT. These solutions leverage cloud computing to provide scalable and flexible remote access capabilities. By hosting SSH servers in the cloud, users can access IoT devices from anywhere in the world without the need for complex infrastructure.
Cloud-based SSH solutions also offer additional features such as centralized management, automated updates, and real-time monitoring. These features make them particularly suitable for large-scale IoT deployments where managing multiple devices can be challenging.
Choosing the Right Remote SSH IoT Solution
Selecting the right Remote SSH IoT solution depends on several factors, including the size of your IoT deployment, your budget, and your security requirements. Below are some key considerations to keep in mind:
- Security: Ensure that the solution provides robust encryption and authentication mechanisms to protect your IoT devices.
- Scalability: Choose a solution that can handle the number of devices in your deployment and scale as your needs grow.
- Ease of Use: Opt for a solution that is user-friendly and requires minimal technical expertise to set up and operate.
- Cost: Consider the cost of the solution, including any recurring fees or hidden charges, and ensure it fits within your budget.
By carefully evaluating these factors, you can select a Remote SSH IoT solution that meets your specific needs and requirements.
Securing Your Remote SSH Connections
Securing your Remote SSH IoT connections is crucial to protecting your devices and data from unauthorized access. Below are some best practices for enhancing the security of your SSH connections:
- Use Strong Passwords: Ensure that all SSH accounts have strong, unique passwords to prevent brute-force attacks.
- Enable Key-Based Authentication: Use public key authentication instead of passwords for added security.
- Disable Root Login: Restrict root access to prevent unauthorized users from gaining administrative privileges.
- Update Regularly: Keep your SSH software and IoT devices up to date with the latest security patches and updates.
Implementing these security measures can significantly reduce the risk of breaches and ensure the safety of your IoT devices.
Common Issues and Troubleshooting
While Remote SSH IoT offers numerous benefits, users may encounter issues that can affect their experience. Below are some common issues and their solutions:
- Connection Timeout: Check your network settings and ensure that the SSH port is open and accessible.
- Authentication Failure: Verify your login credentials and ensure that key-based authentication is properly configured.
- Performance Issues: Optimize your SSH settings and reduce the number of simultaneous connections to improve performance.
By addressing these issues promptly, you can ensure smooth and uninterrupted access to your IoT devices.
Case Studies: Real-World Examples
Several organizations have successfully implemented Remote SSH IoT solutions to enhance their operations. Below are some real-world examples:
- Healthcare: A hospital used Remote SSH IoT to securely manage medical devices, enabling real-time monitoring and remote diagnostics.
- Manufacturing: A manufacturing plant implemented SSH tunneling to access and control IoT devices on the factory floor, improving efficiency and reducing downtime.
- Agriculture: A farm utilized cloud-based SSH to remotely monitor and manage IoT sensors, optimizing crop yields and resource usage.
These case studies demonstrate the versatility and effectiveness of Remote SSH IoT in various industries.
Future of Remote SSH IoT
The future of Remote SSH IoT looks promising, with advancements in technology and increasing adoption across industries. Emerging trends such as quantum computing and artificial intelligence are expected to further enhance the capabilities of SSH protocols, making them even more secure and efficient.
As the number of IoT devices continues to grow, the demand for secure and reliable remote access solutions will only increase. Remote SSH IoT is well-positioned to meet this demand, offering scalable and flexible solutions for managing IoT devices.
Best Practices for Remote SSH IoT
To get the most out of your Remote SSH IoT solution, follow these best practices:
- Regularly Audit Your Connections: Monitor SSH connections and activities to detect and address any suspicious behavior.
- Implement Multi-Factor Authentication: Add an extra layer of security by requiring users to provide additional verification before accessing IoT devices.
- Document Your Setup: Keep detailed records of your SSH configuration and settings to facilitate troubleshooting and maintenance.
By adhering to these best practices, you can maximize the benefits of Remote SSH IoT and ensure the security and reliability of your IoT devices.
Conclusion and Next Steps
Remote SSH IoT offers a powerful solution for securely managing IoT devices from anywhere in the world. With its enhanced security, scalability, and ease of use, it is an ideal choice for businesses and individuals seeking reliable remote access capabilities. By selecting the right solution and following best practices, you can optimize your operations and protect your devices from unauthorized access.
We encourage you to explore the various Remote SSH IoT solutions available and find the one that best suits your needs. Don't forget to leave a comment or share this article with others who may find it useful. For more information on IoT and related technologies, check out our other articles on the site.