In today's interconnected world, the Internet of Things (IoT) continues to revolutionize the way we interact with technology. Managing IoT devices remotely through Secure Shell (SSH) is essential for maintaining security and efficiency. This article dives deep into how AWS can help you establish secure SSH connections to IoT devices located anywhere in the world.
As IoT deployments grow in scale and complexity, ensuring secure access becomes paramount. SSH, a cryptographic network protocol, plays a critical role in facilitating secure remote access. By leveraging AWS services, organizations can implement robust solutions that enhance both security and scalability.
This guide will walk you through the steps to set up SSH access to IoT devices using AWS, providing practical examples and best practices to ensure your implementation meets industry standards. Whether you're a developer, IT professional, or simply curious about IoT security, this article has something for everyone.
Read also:Araujo Onlyfans A Comprehensive Guide To Her Content Journey And Success
Table of Contents
- Introduction to SSH and IoT Security
- Benefits of Using AWS for IoT SSH
- Overview of Setting Up SSH on AWS
- Managing IoT Devices with AWS IoT Core
- Creating an SSH Tunnel with AWS
- Security Best Practices for SSH on AWS
- Example Implementation of SSH on AWS
- Troubleshooting Common Issues
- Scaling SSH Access for Large IoT Deployments
- Conclusion and Next Steps
Introduction to SSH and IoT Security
Secure Shell (SSH) is a fundamental protocol for secure remote communication. When applied to IoT devices, SSH ensures that data transmitted between devices and servers remains encrypted and protected from unauthorized access.
AWS provides a comprehensive suite of tools and services to facilitate secure SSH connections. By combining AWS IoT Core, EC2 instances, and other services, organizations can create scalable and secure environments for managing IoT devices.
Understanding the importance of SSH in IoT security is crucial. As cyber threats continue to evolve, implementing robust security measures becomes imperative for protecting sensitive data and maintaining operational integrity.
Benefits of Using AWS for IoT SSH
AWS offers several advantages for managing SSH connections to IoT devices:
- Scalability: AWS allows you to scale your SSH infrastructure seamlessly, accommodating growing IoT fleets.
- Security: AWS provides advanced security features, including identity and access management (IAM), to protect your IoT devices.
- Global Reach: With AWS's global infrastructure, you can connect to IoT devices located anywhere in the world.
- Integration: AWS services integrate effortlessly, enabling you to build end-to-end solutions for IoT management.
These benefits make AWS an ideal choice for organizations seeking to enhance their IoT security posture while maintaining flexibility and scalability.
Overview of Setting Up SSH on AWS
Understanding the Components
Setting up SSH access to IoT devices on AWS involves several key components:
Read also:How To Die Painlessly A Comprehensive Guide To Understanding Endoflife Choices
- AWS IoT Core: A managed service for connecting IoT devices to the cloud.
- EC2 Instances: Virtual servers that act as SSH gateways for IoT devices.
- VPC: Virtual private cloud to ensure secure network isolation.
- Security Groups: Configurations that control inbound and outbound traffic to your EC2 instances.
Step-by-Step Setup
Here's a high-level overview of the setup process:
- Create an AWS account and set up necessary services.
- Provision an EC2 instance to act as an SSH gateway.
- Configure security groups to allow SSH traffic.
- Connect IoT devices to AWS IoT Core.
- Establish SSH connections from the gateway to IoT devices.
This setup ensures secure and efficient communication between your IoT devices and the cloud.
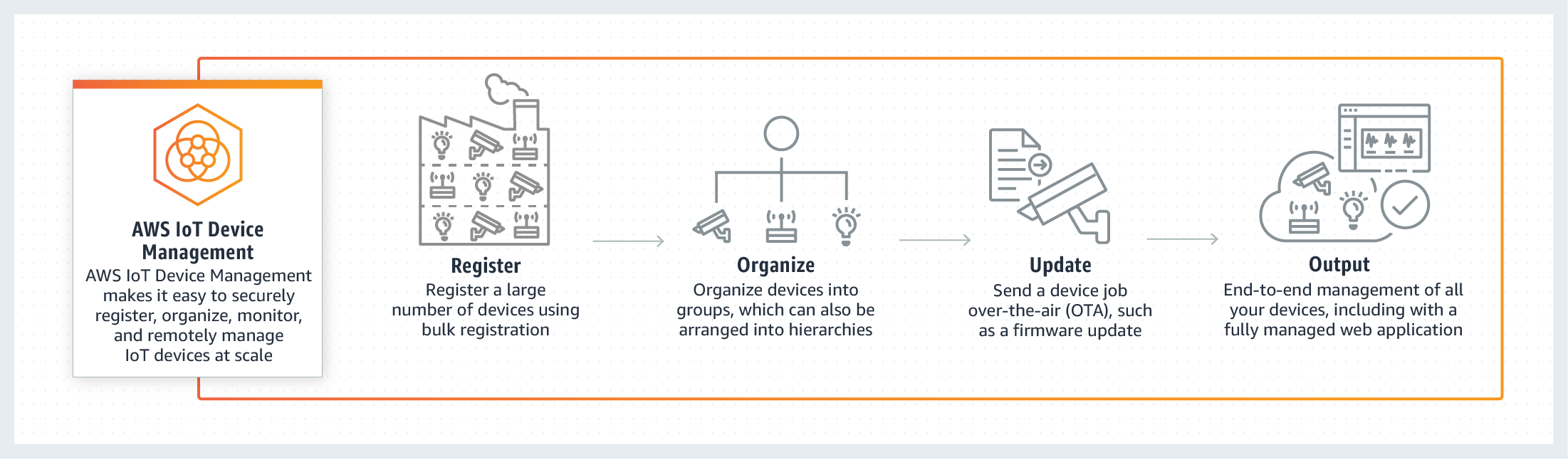
Managing IoT Devices with AWS IoT Core
AWS IoT Core is a central component for managing IoT devices. It enables secure and reliable communication between devices and the cloud, making it ideal for SSH implementations.
Key features of AWS IoT Core include:
- Device Shadowing: Maintaining a virtual representation of device state.
- Rules Engine: Automating data processing and integration with other AWS services.
- Certificate Management: Simplifying the process of securing device connections.
By leveraging these features, organizations can streamline the management of their IoT devices while ensuring secure SSH access.
Creating an SSH Tunnel with AWS
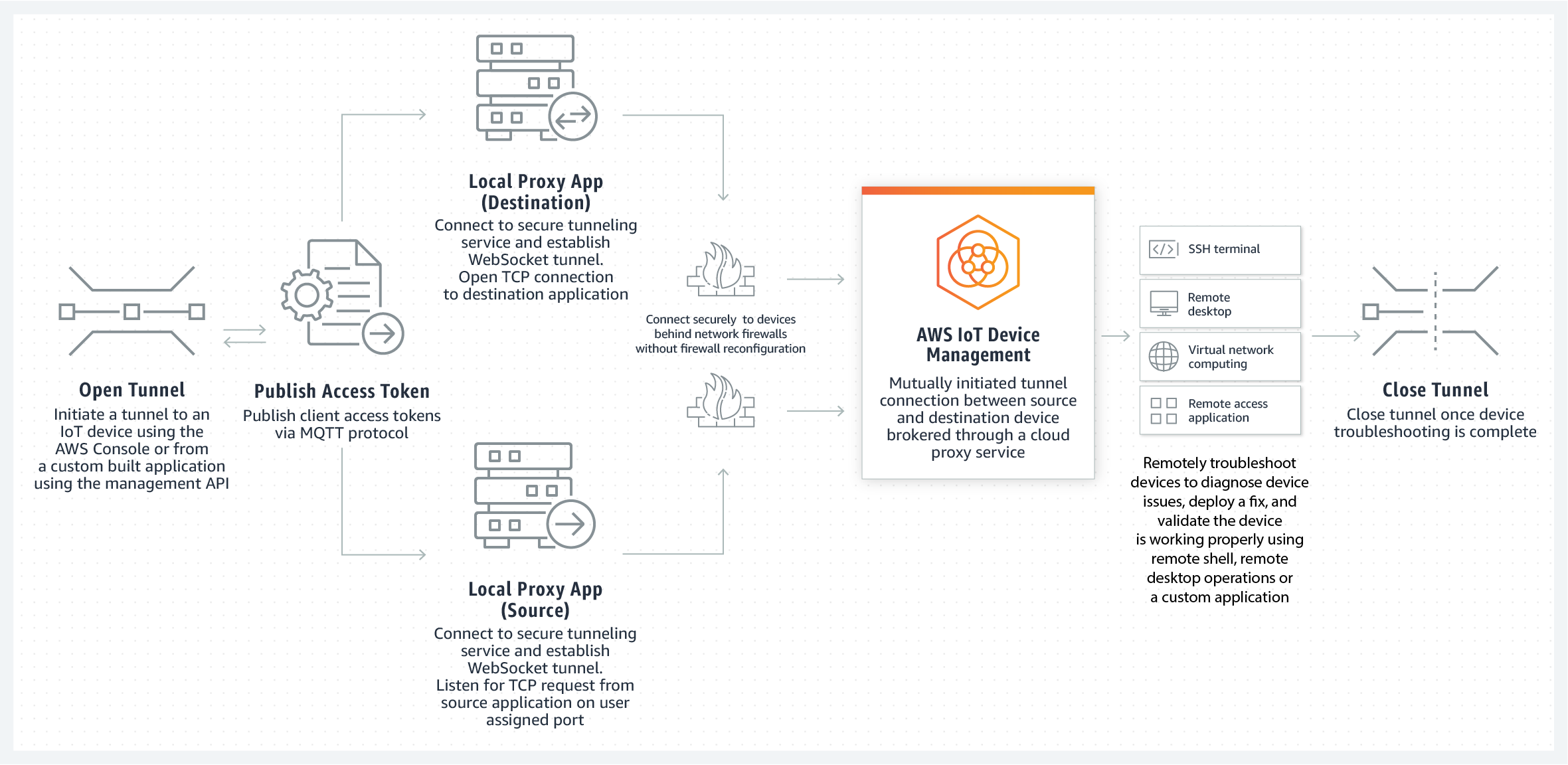
What is an SSH Tunnel?
An SSH tunnel is a method of securely forwarding data between two endpoints. In the context of IoT, SSH tunnels enable secure communication between devices and the cloud.
Steps to Create an SSH Tunnel
To create an SSH tunnel with AWS, follow these steps:
- Set up an EC2 instance as the SSH gateway.
- Generate SSH keys for secure authentication.
- Configure the SSH client to establish a tunnel to the gateway.
- Forward traffic through the tunnel to your IoT devices.
By implementing SSH tunnels, you can ensure that all communication between your IoT devices and the cloud remains encrypted and secure.
Security Best Practices for SSH on AWS
Implementing security best practices is essential for protecting your IoT devices and SSH connections. Consider the following recommendations:
- Use Strong Passwords and Keys: Ensure that all SSH credentials are strong and unique.
- Enable Two-Factor Authentication: Add an extra layer of security to your SSH connections.
- Regularly Update Software: Keep your devices and servers updated with the latest security patches.
- Monitor Logs: Use AWS CloudWatch to monitor SSH activity and detect potential threats.
By following these best practices, you can significantly reduce the risk of security breaches and protect your IoT infrastructure.
Example Implementation of SSH on AWS
Here's a practical example of setting up SSH access to an IoT device using AWS:
1. Launch an EC2 instance in your AWS account.
2. Configure the security group to allow SSH traffic on port 22.
3. Connect your IoT device to AWS IoT Core using MQTT or HTTP protocols.
4. Use the SSH client on your local machine to establish a connection to the EC2 instance.
5. Forward traffic from the EC2 instance to your IoT device using SSH tunneling.
This example demonstrates how AWS services can be combined to create a secure and efficient SSH solution for IoT devices.
Troubleshooting Common Issues
When working with SSH on AWS, you may encounter various issues. Here are some common problems and their solutions:
- Connection Errors: Verify that security groups and network settings allow SSH traffic.
- Authentication Failures: Ensure that SSH keys are correctly configured and match between the client and server.
- Performance Issues: Optimize your EC2 instance type and network configuration for better performance.
By addressing these issues promptly, you can ensure smooth operation of your SSH setup.
Scaling SSH Access for Large IoT Deployments
As your IoT fleet grows, scaling SSH access becomes critical. AWS provides several options for scaling:
- Auto Scaling Groups: Automatically adjust the number of EC2 instances based on demand.
- Elastic Load Balancing: Distribute SSH traffic across multiple instances for better performance.
- Managed Services: Utilize AWS-managed services to simplify scaling and reduce operational overhead.
By leveraging these scaling strategies, you can ensure that your SSH infrastructure remains robust and efficient as your IoT deployment expands.
Conclusion and Next Steps
In conclusion, securing SSH access to IoT devices using AWS is a powerful solution for organizations looking to enhance their IoT security. By following the steps and best practices outlined in this article, you can create a secure and scalable SSH infrastructure that meets the demands of modern IoT deployments.
We invite you to take the next steps by:
- Exploring AWS services in greater detail.
- Testing the SSH setup in a development environment.
- Sharing your experiences and insights in the comments section below.
Thank you for reading, and we hope this article has provided valuable insights into securing IoT devices with SSH on AWS.