In today's interconnected world, the ability to access IoT devices securely through SSH on AWS has become a critical skill for developers and IT professionals. Whether you're managing smart home devices, industrial equipment, or any other IoT infrastructure, understanding how to leverage AWS for remote access can significantly enhance your operational capabilities. This article will guide you step-by-step through the process of setting up and maintaining secure IoT SSH connections on AWS.
As more organizations adopt IoT technologies, the demand for robust security measures continues to grow. AWS provides a scalable and secure platform to manage IoT devices, ensuring that data remains protected while enabling seamless remote access. This guide aims to provide practical insights into how you can utilize AWS services to establish and maintain secure SSH connections with your IoT devices.
Whether you're a beginner or an experienced professional, this article will equip you with the knowledge and tools necessary to streamline your IoT management processes. Let's dive into the details and explore how you can leverage AWS for secure IoT SSH access.
Read also:Filmyflypi Your Ultimate Guide To Streaming Movies Online
Table of Contents
- Introduction to IoT SSH AWS
- Why Choose AWS for IoT SSH?
- Setting Up AWS IoT Core
- Configuring SSH Access
- Securing IoT SSH Connections
- Best Practices for IoT SSH on AWS
- Troubleshooting Common Issues
- Case Studies and Examples
- Future Trends in IoT SSH AWS
- Conclusion and Next Steps
Introduction to IoT SSH AWS
IoT SSH AWS refers to the process of securely accessing IoT devices using SSH (Secure Shell) through Amazon Web Services. SSH is a network protocol that allows users to securely connect to remote devices over an unsecured network. AWS provides a comprehensive suite of tools and services to facilitate this process, ensuring that your IoT devices remain secure and accessible.
What is IoT?
The Internet of Things (IoT) refers to a network of interconnected devices that can communicate and exchange data with each other. These devices range from simple sensors to complex machinery, all designed to enhance automation and data collection. IoT devices rely on secure and reliable connections to function effectively, making SSH an essential tool for managing them.
Why Use SSH for IoT Devices?
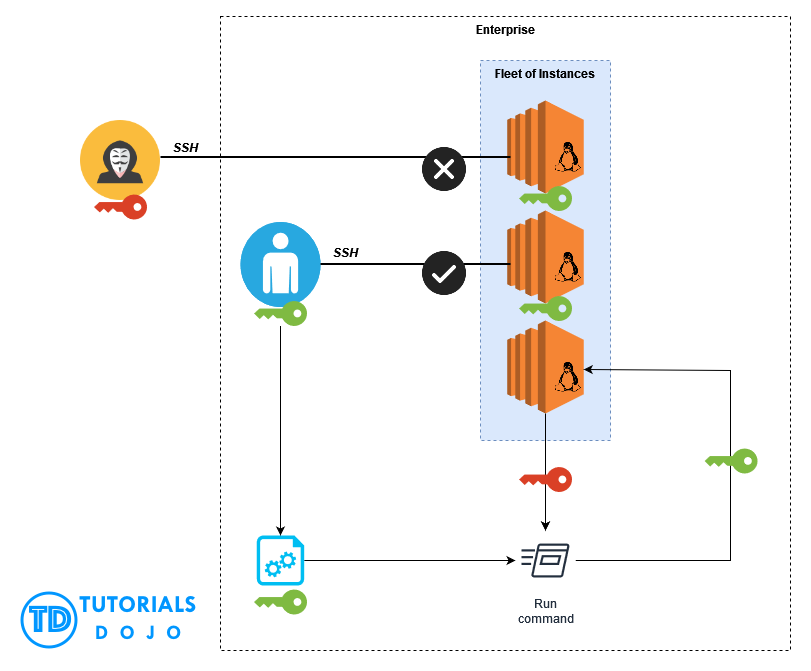
SSH provides a secure and encrypted method for accessing IoT devices remotely. It ensures that sensitive data remains protected from unauthorized access while allowing administrators to manage devices efficiently. By leveraging AWS, organizations can scale their IoT infrastructure and maintain secure connections without compromising performance.
Why Choose AWS for IoT SSH?
AWS offers several advantages for managing IoT SSH connections. Its robust infrastructure, coupled with advanced security features, makes it an ideal platform for organizations looking to streamline their IoT operations.
- Scalability: AWS allows you to scale your IoT infrastructure based on demand, ensuring that your devices remain accessible regardless of traffic levels.
- Security: AWS provides end-to-end encryption and advanced security protocols to protect your IoT devices from potential threats.
- Integration: AWS IoT Core integrates seamlessly with other AWS services, enabling you to create a comprehensive ecosystem for managing your IoT devices.
Setting Up AWS IoT Core
AWS IoT Core is a managed cloud service that allows connected devices to interact with cloud applications and other devices. To set up AWS IoT Core for SSH access, follow these steps:
Step 1: Create an AWS Account
If you don't already have an AWS account, sign up for one at https://aws.amazon.com/. AWS offers a free tier for new users, allowing you to experiment with its services without incurring costs.
Read also:Shyna Khatri Web A Comprehensive Guide To Her Digital Presence
Step 2: Configure AWS IoT Core
Once your account is set up, navigate to the AWS Management Console and select AWS IoT Core. From there, you can configure settings such as device certificates, policies, and rules to manage your IoT devices effectively.
Configuring SSH Access
Configuring SSH access for IoT devices on AWS involves several steps. Below is a detailed guide to help you set up secure SSH connections:
Step 1: Install SSH on Your IoT Device
Ensure that your IoT device has an SSH server installed. Most Linux-based devices come with SSH pre-installed, but you may need to install it manually on other platforms.
Step 2: Set Up AWS EC2 Instance
Create an EC2 instance on AWS to act as a bridge between your local machine and the IoT device. This instance will handle the SSH connection and provide a secure channel for communication.
Step 3: Configure Security Groups
Set up security groups to allow SSH traffic between your local machine, the EC2 instance, and the IoT device. Be sure to restrict access to only authorized IP addresses to enhance security.
Securing IoT SSH Connections
Security is paramount when managing IoT devices. Below are some best practices for securing your IoT SSH connections:
- Use strong, unique passwords or SSH keys for authentication.
- Regularly update your IoT devices and SSH software to patch vulnerabilities.
- Monitor network traffic for suspicious activity and implement intrusion detection systems.
Best Practices for IoT SSH on AWS
To ensure optimal performance and security when managing IoT devices with SSH on AWS, consider the following best practices:
Optimize Resource Usage
Monitor resource usage on your EC2 instances and IoT devices to ensure they are operating efficiently. Use AWS CloudWatch to track metrics and set up alerts for any anomalies.
Implement Role-Based Access Control
Limit access to your IoT devices by implementing role-based access control (RBAC). This ensures that only authorized personnel can manage and interact with your devices.
Troubleshooting Common Issues
Despite careful planning, issues may arise when setting up IoT SSH connections on AWS. Below are some common problems and their solutions:
Connection Timeout
If you encounter connection timeouts, check your security group settings to ensure that SSH traffic is allowed. Additionally, verify that your IoT device is properly configured and reachable from the EC2 instance.
Authentication Failure
Authentication failures can occur due to incorrect credentials or misconfigured SSH keys. Double-check your login details and ensure that your SSH keys are correctly installed on both the IoT device and EC2 instance.
Case Studies and Examples
Several organizations have successfully implemented IoT SSH solutions on AWS. For example, a manufacturing company used AWS IoT Core and SSH to remotely monitor and manage its factory equipment, resulting in significant cost savings and improved efficiency.
Future Trends in IoT SSH AWS
As IoT technologies continue to evolve, so too will the methods for managing them. Future trends in IoT SSH AWS include:
- Increased adoption of quantum-resistant encryption to protect against emerging cyber threats.
- Integration with artificial intelligence and machine learning for predictive maintenance and automated decision-making.
- Expansion of edge computing capabilities to reduce latency and improve performance for IoT devices.
Conclusion and Next Steps
In conclusion, accessing IoT devices through SSH on AWS is a powerful way to manage and secure your IoT infrastructure. By following the steps outlined in this guide, you can set up and maintain secure connections that enhance your operational capabilities.
We encourage you to take the next step by experimenting with AWS IoT Core and SSH to see how it can benefit your organization. Don't forget to leave a comment below sharing your experiences or questions. Additionally, consider exploring other articles on our site for more insights into IoT and cloud computing.
Remember, the future of IoT lies in secure and scalable solutions, and AWS provides the tools you need to succeed. Start your journey today!