In the rapidly evolving world of technology, Remote SSH IoT (Internet of Things) is emerging as a critical solution for connecting and managing devices remotely. Whether you're a developer, hobbyist, or professional, understanding how to configure and secure IoT devices via SSH is essential. In this article, we'll delve into the intricacies of remote SSH IoT behind examples, offering practical insights and actionable advice.
As the Internet of Things continues to expand, remote access to devices has become indispensable. This capability allows users to monitor, troubleshoot, and manage IoT devices from virtually anywhere. By leveraging SSH (Secure Shell), a secure communication protocol, you can achieve seamless connectivity while ensuring robust security.
This article is designed to provide a deep dive into remote SSH IoT configurations, examples, and best practices. Whether you're looking to implement IoT solutions in smart homes, industrial automation, or agriculture, you'll find valuable information to guide your journey.
Read also:Pining Kim By Trailblazer An Indepth Look At Her Journey Achievements And Impact
Table of Contents
- Understanding Remote SSH IoT
- What is SSH?
- Remote SSH IoT Behind Examples
- Setting Up SSH for IoT Devices
- Security Measures for Remote SSH IoT
- Common Issues and Troubleshooting
- Best Practices for Remote SSH IoT
- Applications of Remote SSH IoT
- Future Trends in Remote SSH IoT
- Conclusion and Next Steps
Understanding Remote SSH IoT
Definition and Importance
Remote SSH IoT refers to the use of Secure Shell (SSH) to access and manage IoT devices remotely. This technology plays a pivotal role in enabling secure and efficient communication between devices, particularly in scenarios where physical access is limited or impractical.
SSH provides an encrypted channel for data transmission, ensuring that sensitive information remains protected from unauthorized access. As IoT adoption grows, so does the need for reliable remote management solutions, making SSH an indispensable tool for modern IoT systems.
What is SSH?
Overview of Secure Shell Protocol
SSH, or Secure Shell, is a cryptographic network protocol used to establish secure connections between a client and a server. It was designed to replace less secure protocols such as Telnet and rlogin, offering robust encryption, authentication, and integrity protection.
Key features of SSH include:
- Strong encryption for data in transit
- Public key authentication for secure login
- Support for various services, including file transfers and command execution
Remote SSH IoT Behind Examples
Practical Use Cases
There are numerous examples of how remote SSH IoT can be implemented across different industries. Below are some real-world applications:
- Smart Home Automation: Control and monitor smart home devices such as lighting, thermostats, and security systems from anywhere.
- Industrial IoT (IIoT): Remotely manage sensors, actuators, and other equipment in manufacturing environments for improved efficiency and reduced downtime.
- Agricultural Monitoring: Use IoT devices equipped with SSH to track soil moisture, temperature, and other environmental factors in real-time.
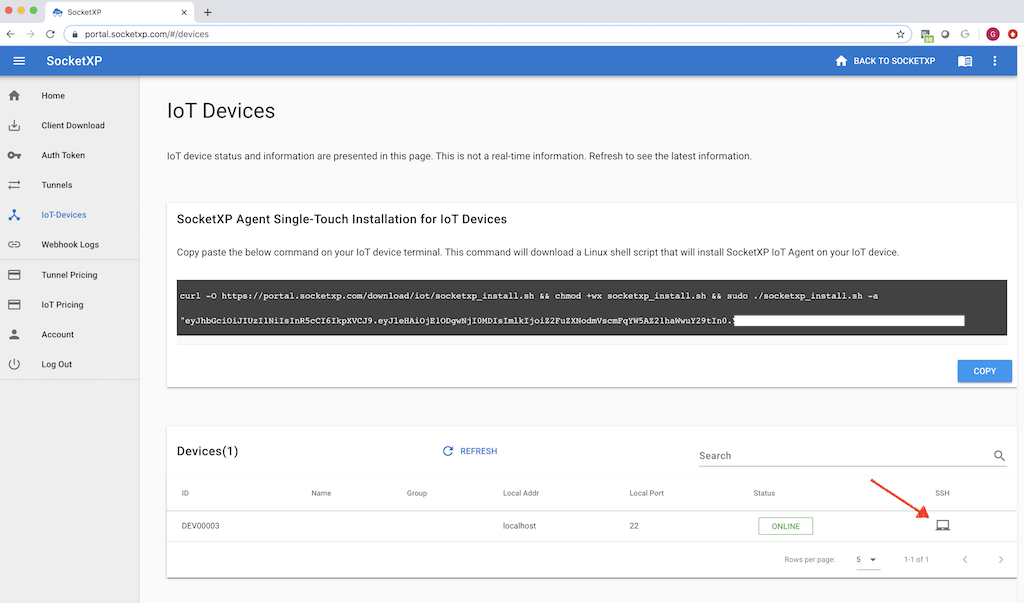
Setting Up SSH for IoT Devices
Step-by-Step Guide
Setting up SSH for IoT devices involves several key steps. Follow this guide to ensure a smooth and secure configuration:
Read also:Ullu Web Series New 2024 The Ultimate Guide To Indias Hottest Streaming Sensation
- Install SSH Server: Ensure that your IoT device has an SSH server installed. For Linux-based systems, OpenSSH is commonly used.
- Configure Firewall Settings: Open the necessary ports (default is 22) to allow SSH traffic while maintaining security.
- Set Up Public Key Authentication: Generate and deploy public/private key pairs to eliminate the need for password-based authentication.
- Test the Connection: Use an SSH client (such as PuTTY or OpenSSH) to establish a connection and verify functionality.
Security Measures for Remote SSH IoT
Best Practices for Securing SSH Connections
Security is paramount when implementing remote SSH IoT solutions. Here are some essential measures to safeguard your devices:
- Use Strong Passwords: If password-based authentication is used, ensure that passwords are complex and unique.
- Enable Two-Factor Authentication (2FA): Add an extra layer of security by requiring a second form of verification.
- Regularly Update Software: Keep your SSH server and related software up to date to protect against vulnerabilities.
- Monitor Logs: Regularly review SSH logs to detect and respond to suspicious activities.
Common Issues and Troubleshooting
Solving Connection Problems
While SSH is a reliable protocol, issues can arise. Below are some common problems and their solutions:
- Connection Refused: Ensure that the SSH server is running and that the correct IP address and port are being used.
- Authentication Failed: Double-check your credentials or public key configuration.
- Timeout Errors: Verify network connectivity and firewall settings.
Best Practices for Remote SSH IoT
Optimizing Performance and Security
Adhering to best practices can significantly enhance the performance and security of your remote SSH IoT setup:
- Limit Access: Restrict SSH access to trusted IP addresses or networks.
- Use Non-Standard Ports: Change the default SSH port to reduce the risk of brute-force attacks.
- Implement Role-Based Access Control (RBAC): Assign specific permissions to users based on their roles and responsibilities.
Applications of Remote SSH IoT
Industry-Specific Use Cases
Remote SSH IoT finds applications across various sectors. Below are some notable examples:
- Healthcare: Monitor medical devices and patient data remotely for improved healthcare delivery.
- Retail: Manage point-of-sale (POS) systems and inventory tracking devices from a centralized location.
- Transportation: Enable real-time monitoring and control of vehicles and infrastructure for enhanced safety and efficiency.
Future Trends in Remote SSH IoT
Emerging Technologies and Innovations
As technology continues to evolve, several trends are shaping the future of remote SSH IoT:
- Edge Computing: Processing data closer to the source reduces latency and improves response times.
- Quantum-Safe Cryptography: Developing encryption methods that remain secure in the face of quantum computing advancements.
- AI and Machine Learning: Leveraging AI for predictive maintenance and anomaly detection in IoT systems.
Conclusion and Next Steps
In conclusion, remote SSH IoT is a powerful tool that enables secure and efficient management of IoT devices. By understanding the principles, configurations, and security measures outlined in this article, you can harness the full potential of SSH for your IoT projects.
We invite you to take the following actions:
- Leave a comment below sharing your thoughts or questions about remote SSH IoT.
- Explore other articles on our site for more insights into IoT and related technologies.
- Stay updated with the latest trends and innovations in the field of remote SSH IoT.
Thank you for reading, and we look forward to hearing your feedback!
Source: SSH Protocol Overview | IoT For All