SSH access for IoT devices has become increasingly important as the Internet of Things continues to expand. As more devices become interconnected, ensuring secure communication and remote management is crucial. This article will explore everything you need to know about SSH access for IoT devices, including setup, best practices, and security considerations.
With billions of IoT devices now deployed worldwide, managing and securing these devices remotely is no longer optional but essential. From smart home appliances to industrial automation systems, SSH plays a pivotal role in maintaining secure connections. This guide aims to provide in-depth knowledge to help you leverage SSH effectively for your IoT projects.
Whether you're a developer, system administrator, or security professional, understanding SSH access for IoT devices is critical to ensuring the integrity and security of your network. Let's dive into the details and explore how you can implement SSH securely and efficiently.
Read also:Vivian Jenna Wilson A Rising Star In The Entertainment World
Table of Contents
- Introduction to SSH Access for IoT Devices
- What is SSH?
- Why Use SSH for IoT Devices?
- Setting Up SSH Access for IoT Devices
- Security Best Practices for SSH Access
- Common SSH Commands for IoT Management
- Troubleshooting SSH Access Issues
- Tools for Managing SSH in IoT
- Case Studies: Real-World Examples of SSH in IoT
- The Future of SSH in IoT
Introduction to SSH Access for IoT Devices
SSH, or Secure Shell, is a cryptographic network protocol used for secure data communication. When it comes to IoT devices, SSH access allows administrators and developers to manage and interact with devices remotely while maintaining a high level of security. IoT devices often operate in remote or inaccessible locations, making SSH a vital tool for efficient management.
Importance of SSH in IoT
As IoT ecosystems grow in complexity, the need for secure communication protocols becomes paramount. SSH provides encryption, authentication, and data integrity, ensuring that sensitive information transmitted between devices and servers remains protected. This section will delve deeper into why SSH is indispensable for IoT deployments.
What is SSH?
SSH is a protocol designed to secure network services against unauthorized access. It uses public-key cryptography to authenticate remote users and encrypts all data transmitted between the client and server. For IoT devices, SSH serves as a secure channel for configuration, monitoring, and troubleshooting.
Key Features of SSH
- Encryption: Protects data from eavesdropping.
- Authentication: Ensures only authorized users can access the system.
- Data Integrity: Prevents tampering during transmission.
Why Use SSH for IoT Devices?
IoT devices are often resource-constrained, yet they require robust security measures. SSH is lightweight, efficient, and highly secure, making it an ideal choice for IoT applications. This section will explore the specific advantages of using SSH for IoT devices, including ease of deployment, compatibility, and scalability.
Advantages Over Other Protocols
Compared to other protocols like Telnet, SSH offers superior security and reliability. While Telnet transmits data in plain text, SSH encrypts all communications, safeguarding sensitive information. This subsection will compare SSH with alternative protocols and highlight its strengths.
Setting Up SSH Access for IoT Devices
Configuring SSH access for IoT devices involves several steps, including enabling the SSH server, generating keys, and configuring firewall rules. This section will walk you through the process step-by-step, ensuring a secure and functional setup.
Read also:Filmyflypi Your Ultimate Guide To Streaming Movies Online
Step-by-Step Guide
- Enable SSH on your IoT device.
- Generate public and private keys.
- Configure SSH settings for optimal security.
- Test the connection to ensure everything works correctly.
Security Best Practices for SSH Access
While SSH is inherently secure, improper configuration can expose vulnerabilities. This section will outline best practices for securing SSH access in IoT environments, including disabling password authentication, using strong keys, and implementing fail2ban.
Common Security Threats
Brute force attacks, man-in-the-middle attacks, and unauthorized access are among the most common threats to SSH-enabled IoT devices. Understanding these risks and taking proactive measures can significantly enhance the security of your IoT network.
Common SSH Commands for IoT Management
Once SSH access is established, administrators can use various commands to manage and monitor IoT devices. This section will provide a list of essential SSH commands and explain their functions, helping you streamline your IoT management tasks.
Examples of Useful Commands
- ssh user@hostname: Connect to a remote device.
- scp file user@hostname:/path: Transfer files securely.
- ssh-keygen: Generate public and private keys.
Troubleshooting SSH Access Issues
Despite its reliability, SSH access can sometimes encounter issues such as connection failures or authentication errors. This section will address common problems and provide solutions to help you resolve them quickly and effectively.
Tips for Resolving Connection Issues
Check firewall settings, verify key configurations, and ensure the SSH service is running. These steps can help identify and fix most SSH-related issues. Additionally, consulting the device's logs can provide valuable insights into the root cause of the problem.
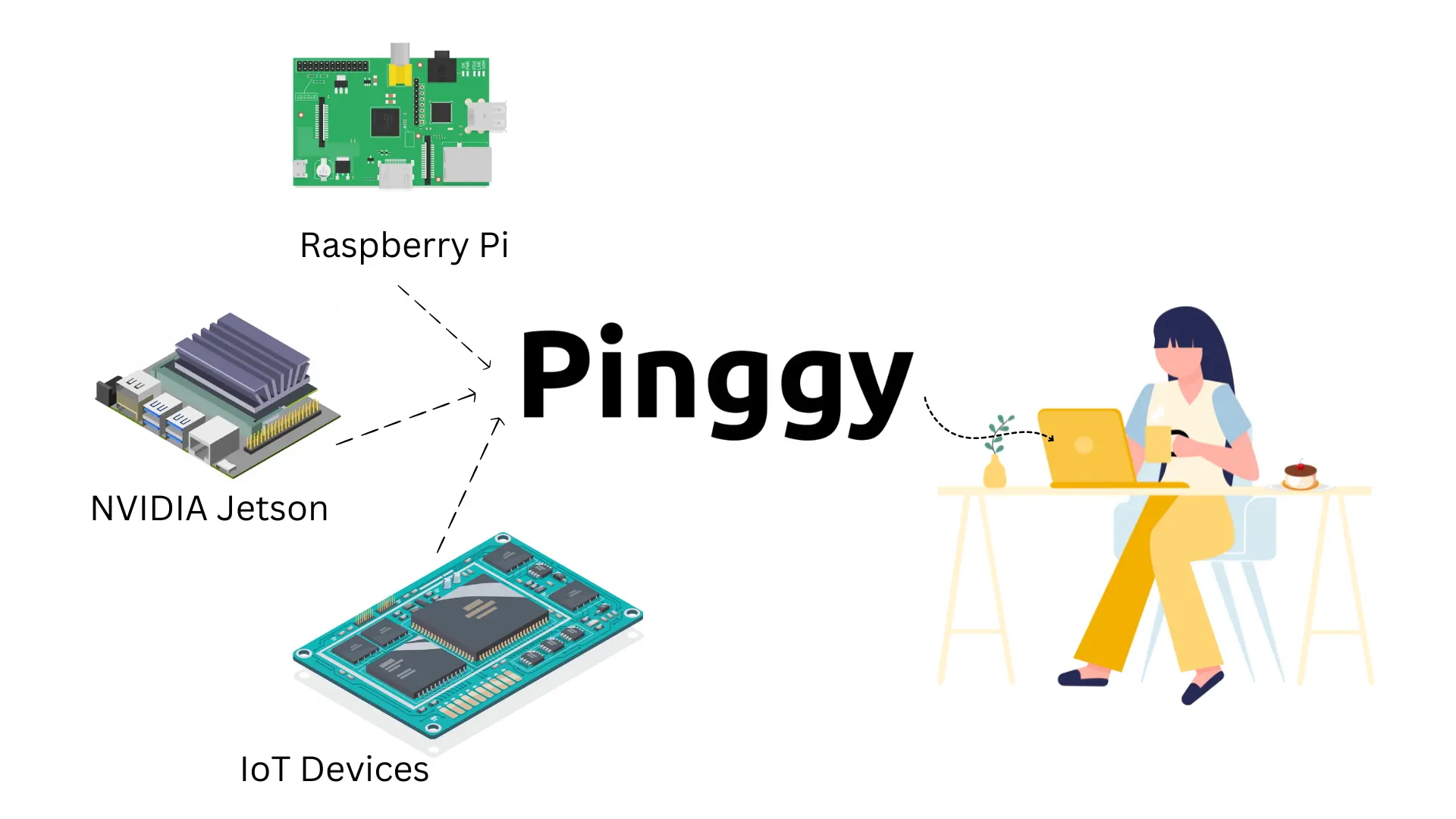
Tools for Managing SSH in IoT
Several tools and platforms are available to simplify SSH management for IoT devices. This section will introduce some of the most popular tools, including PuTTY, OpenSSH, and SSHFS, and explain how they can enhance your IoT management capabilities.
Comparison of Popular Tools
- PuTTY: A widely-used SSH client for Windows.
- OpenSSH: A free and open-source SSH suite for Unix-like systems.
- SSHFS: Allows mounting remote filesystems over SSH.
Case Studies: Real-World Examples of SSH in IoT
Examining real-world applications of SSH in IoT can provide valuable insights into its practical use. This section will present case studies from various industries, showcasing how organizations leverage SSH to manage and secure their IoT deployments.
Industrial IoT Deployment
A manufacturing company used SSH to remotely configure and monitor hundreds of IoT sensors on its factory floor, reducing downtime and improving operational efficiency.
The Future of SSH in IoT
As IoT technology continues to evolve, so too will the role of SSH in securing these networks. This section will explore emerging trends and advancements in SSH technology, including quantum-resistant cryptography and automated key management.
Challenges and Opportunities
While SSH remains a cornerstone of IoT security, challenges such as key management and scalability must be addressed. However, these challenges also present opportunities for innovation and improvement in the field.
Conclusion
In conclusion, SSH access for IoT devices is an essential component of modern IoT deployments. By understanding its capabilities and implementing best practices, you can ensure the security and efficiency of your IoT network. We encourage you to apply the knowledge gained from this guide and share your experiences in the comments below. Additionally, feel free to explore other articles on our site for further insights into IoT and related technologies.
Thank you for reading, and we hope this article has been informative and helpful in your IoT journey!